How to Simplify Network Access Control With Tanium Network Quarantine Service and Cisco® ISE
How to Simplify Network Access Control With Tanium Network Quarantine Service and Cisco® ISE
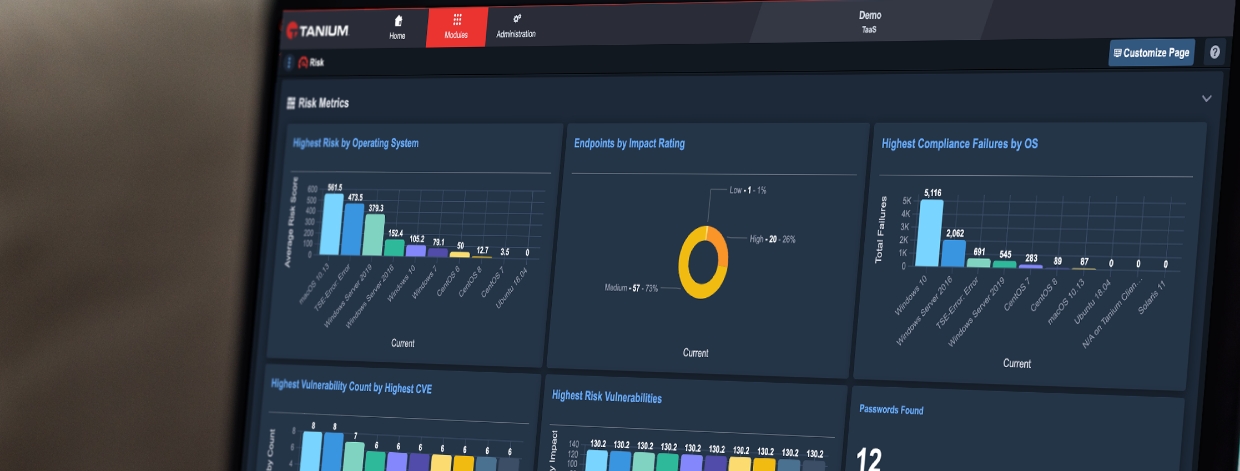
Threat, security compliance and vulnerability data shouldn’t just be captured in alerts and reports – it should help drive the enforcement of tangible security controls. That includes managing which systems are allowed onto your networks and whether they can communicate with other devices based on the risk they present to your environment. It also includes whether they’re allowed to stay connected to your network. “Comply to connect” cannot be a one-time function; organizations need the flexibility to continuously re-evaluate endpoint state and enforce appropriate network controls when systems require remediation.
To achieve this, many organizations rely on a fleet of dedicated Network Access Control (NAC) products in the form of physical or virtual devices that plug into every switch and router on their network. But these architectures are cumbersome, and managing them can be a lot of work, especially at scale. That challenge led us to extend the Tanium platform with what we call Network Quarantine Service (NQS).
NQS allows Tanium to interoperate with network access control technologies, including Cisco ® Identity Service Engine (ISE), via pxGrid. Through integration with Tanium’s core platform and product modules, users can enact network isolation policies against any device, review audit records of prior quarantine actions, and remove quarantines as appropriate.
Policy enforcement made easy
NQS provides a powerful policy enforcement capability that allows any endpoint attribute to trigger a network quarantine enforced by Cisco ISE. Tanium’s broad visibility into asset information, compliance, vulnerabilities, configuration and threats can be the basis of rules, such as:
- Out of date anti-virus signatures
- Missing critical patches
- High-risk open vulnerabilities
- Detected threats
- Critical configuration violations
- Missing essential software
- Unauthorized local account configuration
Several Tanium modules, including Discover, Comply, Patch and Threat Response, can all support NQS use-cases. Customers can also define their own customizable use-cases using the Tanium platform’s content authoring capabilities.
When Tanium identifies a rule violation, NQS can be configured to either automatically enforce a quarantine, or to issue a notification and queue the action for administrator approval. Administrators can easily review pending quarantines along with the impacted assets and the rule that was triggered.
Effective quarantine policies should go beyond an “all or nothing” approach to governing network access. NQS rules can interoperate with ISE policies that appropriately isolate an endpoint, permit access to required resources and allow for remediation to take place. Such policies might include: Full Access, Internet Restricted Access, Intranet Only Access, Remediation Access, or Full Isolation/Quarantine.
This dynamic capability can also be applied to individual users or systems that are being targeted. For example, an administrator might opt to restrict a remote user to remediation access if they are missing a number of critical patches, instead of just restricting a business-critical user to intranet-only access. This allows organizations to maintain business operations while still controlling network access.
Let’s look at what some of these automated rules look like in Tanium
The Automated Rules section of NQS lists all of the defined rules, whether they are active or disabled, and whether they have violations pending approval.

Below is an example of a Automated Policy Rule based on Patch Compliance, targeting systems missing over 10 critical patches. Users can target based on Tanium Computer Groups – in this case, the “All Windows” group.

We’ve set this up to require approval – so when we go back to our homepage we can see all the devices that have violated a rule, and make a decision to quarantine any or all of them.

Of course, we can also remove quarantines – and all of these changes are tracked in an audit log that maintains the user, reason and targeted endpoint.

Conclusion
Network Quarantine Service unifies Tanium’s endpoint visibility with network security technologies like Cisco ISE, ultimately providing a simplified and scalable approach to network access control. If you’re interested in learning more, please reach out to your Technical Account Manager to help with the planning process for implementing NQS.
Cisco is the trademark or registered trademark of Cisco or its affiliates.
Interested in seeing Tanium in action? Schedule a one-to-one demo or attend our weekly webinar. Talk to our Tanium experts at our upcoming events.